代码拉取完成,页面将自动刷新
Recently, our team found an arbitrary order confirm vulnerability in the latest version of the project.
The vulnerability logic is present in the file:
https://gitee.com/old-peanut/wechat_applet__open_source/blob/new/platform-api/src/main/java/com/platform/api/ApiOrderController.java#L246
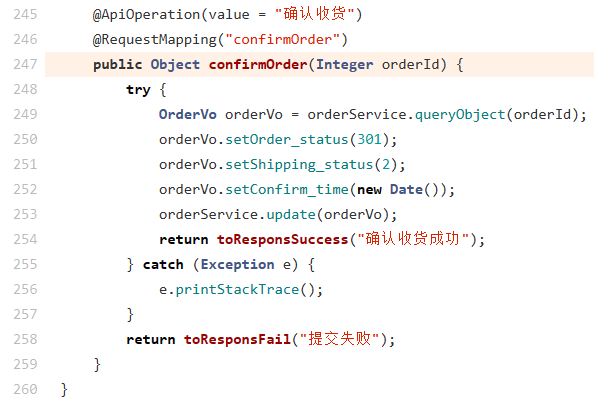
As there is no verification process regarding the ownership of the orderId before updating the order status via orderService.update(), attackers can confirm the receipt status of any order that belong to other users.
To address this vulnerability, we strongly recommend that developers implement access control policies to ensure that only privileged users or the order owner are authorized to perform the operation.